
The 4th edition of RomHack Training is arriving in Rome from September 28 to October 1, 2026. We are hosting six intensive, deep-dive technical courses at the Polo Didattico in Rome.
Whether you are looking to master reverse engineering, web security, mobile/Windows/Linux exploitation, or hardware hacking these sessions are designed to provide hands-on knowledge directly from industry leaders before we head to RomHack Camp on October 2.
Five of our six training sessions will launch with a 10% Early-Bird discount, available until the end of May 2026. Seats are strictly limited to ensure a high-quality instructor-to-student ratio; all tickets include the 4-day course, digital training materials, lunch, and coffee breaks (accommodation is not included in the price).
The training concludes just as RomHack Camp begins at Flaminio Village (October 2 to 4). Every training participant will receive 1 free attendance ticket for the Camp.
Please note: The free ticket covers event entrance only and does not include accommodation. Participants must independently purchase their tent space or bungalow if they wish to stay on-site at the Flaminio Village.
Go from zero to hardware hacking hero. This intensive 4-day training is a deep dive into the marvelous world of Hardware Hacking and Embedded Security. Forget just reading a book—this is a very technically-oriented, hands-on experience where you will get your hands dirty with real-world hardware.
Participants will learn the essential TTPs (Tactics, Techniques, and Procedures) used during professional security audits. From reversing PCBs and identifying “The Good, The Bad & The Ugly” debugging protocols (UART, SPI, JTAG) to dumping firmware from NAND/eMMC memories, we cover the entire hardware attack surface. By the end of the session, you’ll be able to identify, extract, and analyze firmware, performing both static and dynamic analysis to uncover vulnerabilities in the devices that surround us.
9:00 - 18:00
Master PCB reversing, firmware dumping/analysis, and hardware debugging protocols.
Security Researchers, Pentesters, and AppSec professionals curious about Hardware.
Target hardware devices, specialized hacking tools, and all necessary electronic components.

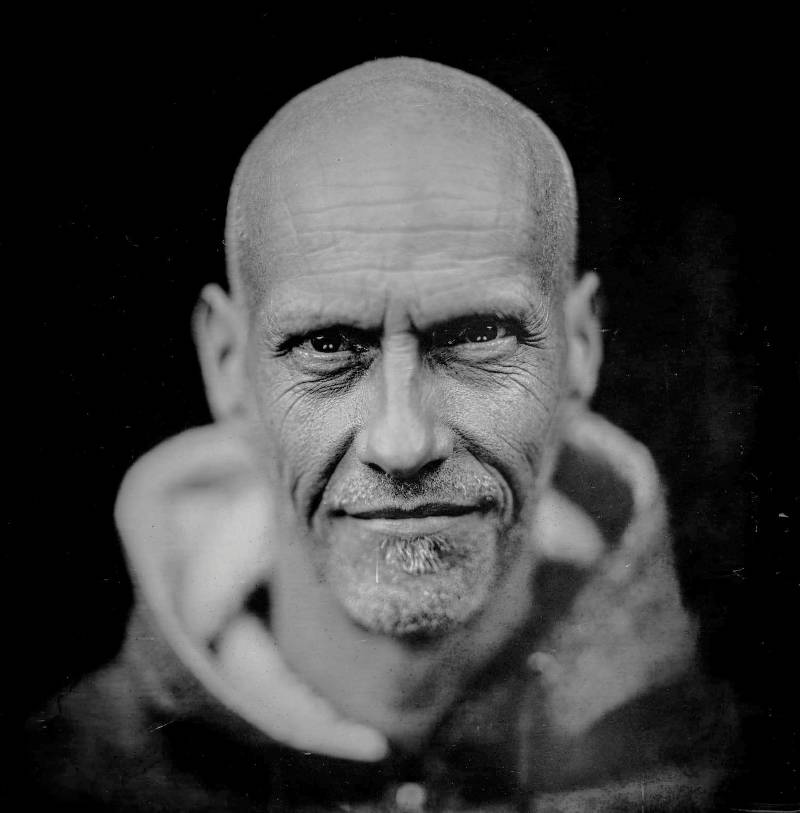
Luca Bongiorni is working as Director of a CyberSecurity Lab and founder of WHID – We Hack In Digsuise (www.whid.ninja). Luca is also actively involved in InfoSec where his main fields of research are: Radio Networks, Hardware Hacking, Internet of Things, and Physical Security. He also loves to share his knowledge and present some cool projects at security conferences around the globe: BlackHat Europe & USA, TROOPERS, HackInParis, DEFCON, HackInBo, RomHack, Defcon Moscow, OWASP Chapters, Security Analyst Summit, etc. At the moment, he is focusing his researches on bypassing biometric access control systems, IIoT Security & Forensics, Air-Gapped Environments and IoOT (Internet of Offensive Things).
Full Price
Early Bird
This 4 day training course will teach you how to exploit advanced .NET enterprise targets, bypass mitigations, chain bugs and pop shellz!
9:00 - 18:00
.NET reverse engineering
bug hunters / vulnerability researchers
course material, virtual machine

Meet Sina Kheirkhah, widely recognized as @SinSinology in the cybersecurity community! Sina is a dedicated full-time vulnerability researcher with a passion for breaking into various systems.
From cracking server-side enterprise solutions to targeting hardware and delving into reverse engineering, Sina‘s expertise covers a wide spectrum. He specializes in low-level exploitation, attacking .NET/Java stacks, bypassing security measures, and chaining bugs seamlessly.
Notably, Sina has competed in Pwn2Own for four consecutive years and has won the “Master of Pwn” title as a solo researcher in pwn2own 2025, demonstrating his dedication to the field.
Full Price
Early Bird
This is a training for Web hackers who want to master their toolbox. Burp Suite Pro is the leading tool for auditing Web applications at large, but also a complex beast where new features get added every few weeks. Mastering Burp Suite Pro, including its newest features, allows testers to get the most out of the tool, optimizing time spent auditing and testing. Work will be faster (hotkeys!) and much more efficient (more tools, more possibilities!). Attendees will also learn to measure and assess the quality of their attacks, a crucial skill in real-life engagements that can make the difference between a false-negative and a critical finding.
9:00 - 18:00
Mastering Burp Pro
bug hunters / vulnerability researchers / penetration testers
course material
lifetime lab access

Nicolas Grégoire has been auditing web apps for 25 years. He is an official Burp Suite Pro trainer since 2015, and has trained more than a thousand people since then, either privately or at public events. Other of that, he runs Agarri, a one-man business where he looks for security vulnerabilities for clients and for fun. His public talks (covering SSRF, XSLT, Burp Suite, …) have been presented at numerous conferences around the world.
Full Price
Early Bird
Widely regarded as the most advanced class on Windows heap exploitation, Corelan Heap doesn’t just teach you how to use known exploits—it teaches you how to conduct your own research. From precise heap folding with “Memorigami” to bypassing the latest Windows 11 mitigations, this 4-day intensive deep-dive covers the entire landscape of modern memory corruption. You will move beyond the stack to master the primary attack surface of today: the Heap.
9:00 - 18:00
Master Windows Heap internals, advanced Feng Shui, and 64-bit exploitation.
Advanced Pentesters, Vulnerability Researchers, and Exploit Developers.
Verbose courseware, custom lab VMs, and life-long post-training support.
Peter Van Eeckhoutte is the founder of Corelan Team and the author of the world-renowned “Exploit Writing Tutorials” series. With decades of experience in the field, he is a recognized authority in Windows exploit development and vulnerability research. Peter is known for his unique ability to break down highly complex low-level concepts into digestible, logical steps, focusing on a “mindset” approach rather than just technical execution. His training has been delivered globally to military, intelligence, and private sector organizations.
Full Price
Early Bird
A 4-day Linux kernel exploitation frenzy!
This training guides researchers through the field of Linux kernel exploitation. In a series of practical labs, the training explores the process of exploiting kernel bugs in a modern Linux distribution on the x86-64 architecture.
The training is structured as a series of lectures, each followed by one or more hands-on labs. The goal of each lab is to write a Linux kernel exploit following the techniques described during the lecture.
The training starts with beginner topics but proceeds into advanced areas as well. The beginner chapters include learning how to escalate privileges and bypass foundational mitigations in x86-64 kernels. The advanced chapters are primarily dedicated to the modern Slab (heap) exploitation techniques and include an in-depth analysis of the kernel allocators’ internals.
The core requirement for this training is the ability to read and write C code. Basic knowledge of the x86-64 architecture and assembly, GDB, and the common binary exploitation techniques would also come in handy. There is no need to know any Linux kernel internals: all required parts are covered during the training.
9:00 - 18:00
exploiting
linux kernel
developers
bug hunters / pentesters
slides/workbook
laboratories (VM)

Andrey Konovalov is a security researcher focusing on the Linux kernel.
Andrey found multiple zero-day bugs in the Linux kernel and published proof-of-concept exploits for these bugs to demonstrate the impact. Andrey contributed to several security-related Linux kernel subsystems and tools: KASAN — a fast dynamic bug detector; syzkaller — a widely-used kernel fuzzer; and Arm Memory Tagging Extension (MTE) — an exploit mitigation.
Andrey gave talks at many security conferences such as OffensiveCon, Zer0Con, Android Security Symposium, and Linux Security Summit. Andrey also maintains a collection of Linux kernel security–related materials and a channel on Linux kernel security.
See xairy.io for all of Andrey’s articles, talks, and projects.
Full Price
Early Bird
Master the art of mobile exploitation in this fast-paced, 4-day intensive training. This course bridges the gap between basic app testing and advanced offensive research, covering everything from the latest iOS 26 architecture to the intricacies of the Android kernel.
Participants will engage in a “learning by doing” curriculum, moving beyond theory to tackle real-world challenges. You will explore advanced mitigations like PAC, PPL, and MTE, while gaining hands-on experience with tools like Frida, Ghidra, and Hopper. A unique highlight for 2026 is the integration of AI-driven techniques and MCP servers to accelerate reversing and forensic analysis. From extracting boot images to building ROP chains and analyzing wild malware, this course delivers the TTPs needed to secure or exploit the devices in everyone’s pocket.
9:00 - 18:00
Advanced iOS/Android reversing, kernel exploitation, and AI-assisted malware analysis.
Pentesters, Mobile Developers, and Security Researchers.
Corellium access, vulnerable app source code, and exploit PoCs.


Prateek is currently working as the Head of Product & Application Security. He has more than 10 years of experience in security research and penetration testing. His core focus area is mobile exploitation, reverse engineering and embedded device security. He is also the author of the open source vulnerable application named Damn Vulnerable iOS app. He has presented and trained at many international conferences including Defcon, POC, TyphoonCon, Blackhat USA, Brucon, Hack in Paris, Phdays, Appsec USA etc. In his free time, he blogs at https://highaltitudehacks.com/.
Dinesh currently leads the Mobile Security Testing Center of Excellence. His core area of expertise is Mobile and Embedded application pentesting and exploitation. He has previously spoken at conferences like Black Hat, Bsides, POC, Def Con, BruCon, AppsecUSA, AppsecEU, HackFest and many more. He maintains multiple open-source intentionally vulnerable Android applications for use by developers and security enthusiasts. He has also authored the guide to Mitigating Risk in IoT systems that covers techniques on security IoT devices and Hacking iOS Applications that covers the known techniques of exploiting iOS applications. Visit http://8ksec.io/blog for technical articles and content by 8kSec Research Team.
Full Price
Early Bird