
€ 4.000,00
€ 3.600,00
The primary objective of this course is to demystify the Windows Heap and provide students with a research-driven mindset. Participants will learn to understand heap managers through experimentation, master precise heap manipulation (including proprietary techniques like Corelan’s Memorigami), and develop reliable exploitation strategies across various bug classes. The course focuses on building fundamental knowledge that remains applicable regardless of OS updates, moving beyond simple “tricks” to a deep technical understanding of memory management.
Check the Heap Training, Testimonials and Clients pages on Corelan web site.
By the end of this session, participants will be able to perform advanced heap feng shui to control memory layouts with precision. They will master the Tactics, Techniques, and Procedures (TTPs) required to bypass modern mitigations like ASLR and DEP using information leaks and ROP chains. Students will leave with the ability to conduct independent heap research on both standard Windows managers (NT and Segment Heap) and proprietary allocators, significantly leveling up their vulnerability research and bug hunting capabilities for both 32-bit and 64-bit architectures.
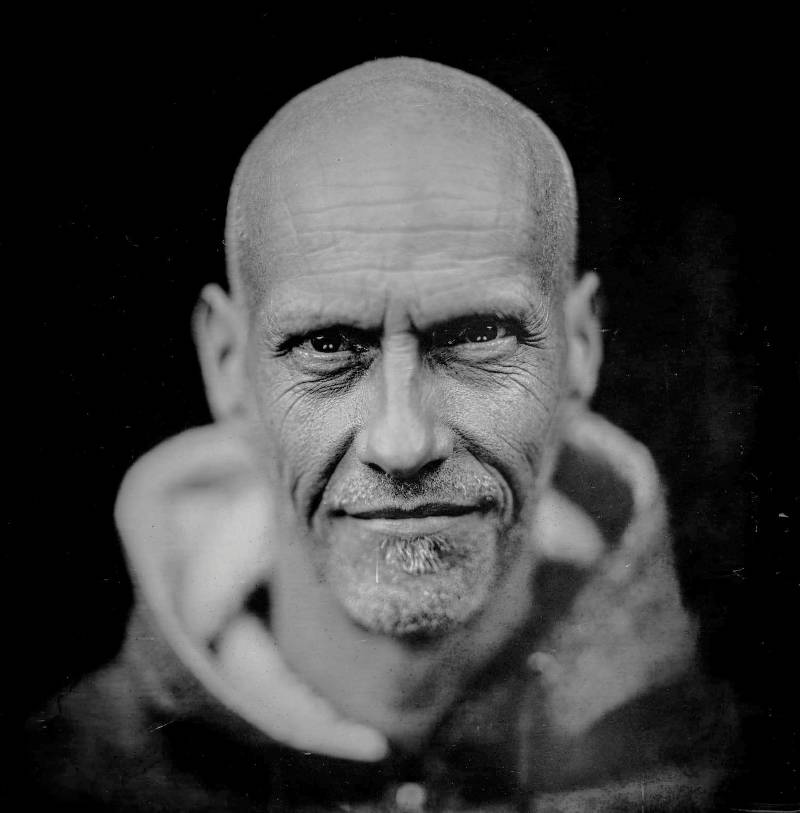
Peter Van Eeckhoutte is the founder of Corelan Team and the author of the world-renowned “Exploit Writing Tutorials” series. With decades of experience in the field, he is a recognized authority in Windows exploit development and vulnerability research. Peter is known for his unique ability to break down highly complex low-level concepts into digestible, logical steps, focusing on a “mindset” approach rather than just technical execution. His training has been delivered globally to military, intelligence, and private sector organizations.
Students must be comfortable reading and writing Python scripts and basic C++ code. A mastery of R.O.P. (Return Oriented Programming) and experience with x86/x64 assembly and debuggers (ideally WinDBG) is mandatory. This is not an entry-level class; you should already have a solid grasp of stack-based exploitation and the drive to solve complex technical problems independently.
Participants must bring a laptop with at least 16GB of RAM and a working installation of VMware or VirtualBox with administrative rights. You will need to pre-configure three specific Lab Virtual Machines (Windows/Linux) based on instructions sent two weeks before the course. A physical notebook for sketching memory layouts and a high level of concentration are also essential for this intensive marathon.
You will receive personalized, verbose courseware and a dedicated personal lab environment with no subscription fees. We provide tons of additional use cases and recent CVEs for post-training study, along with access to private support channels where you can learn at your own pace and interact with Corelan alumni.
• WinDBG Deep Dive: Mastering Classic and WinDBGX for heap exploration.
• Windows Heap Management: Internals of Windows 7, 10, and 11 (NT & Segment Heaps).
• Heap Manipulation: Front-End (FEA) and Back-End (BEA) allocators, Heap Feng Shui, and Memorigami.
• Exploitation Landscape: UAF, Linear/Non-linear overflows, Double Free, and Type Confusion.
• Information Leaks: Strategies to disclose memory layouts and bypass ASLR.
• 64-bit Exploitation: Registers, calling conventions, and building ROP chains on x64.
• Real-world Case Studies: Analyzing and exploiting recent CVEs in 32-bit and 64-bit applications.